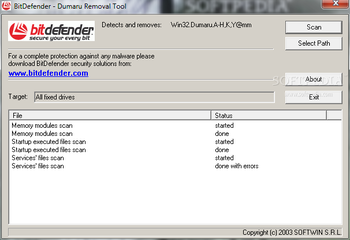
Dumaru Removal Tool is a lightweight application that can completely erase the Win32.Dumaru worm in all its variants.
Win32.Dumaru.A@mm arrives as a fake email from Microsoft:
From: "Microsoft"
[email protected]
Subject: Use this patch immediately !
Body:
Dear friend , use this Internet Explorer patch now!
There are dangerous virus in the Internet now!
More than 500.000 already infected!
Attachment: patch.exe
When executed, the virus will do the following:
Copy itself as:
%SYSTEM%\load32.exe
%WINDOWS%\dllreg.exe
%SYSTEM%\vxdmgr32.exe
Drops and executes a backdoor component
%WINDOWS%\windrv.exe (8192 bytes)
which connects to a IRC server and joins a password protected channel, sends a login notice and waits for the author to issue commands.
Creates the value
"load32"="%SYSTEM%\load32.exe"
in the registry key
[HKLM\Software\Microsoft\Windows\CurrentVersion\Run]
On Windows 9x/Me systems, it does the following:
uses RegisterServiceProcess to hide its presence;
modifies system.ini by adding the entry in the [Boot] section:
shell=explorer.exe %System%\vxdmgr32.exe
modifies win.ini by adding the following entry in the [Windows] section:
run=C:\WINDOWS\dllreg.exe
Harvests e-mail addresses from files matching
*.htm
*.wab
*.html
*.dbx
*.tbb
*.abd
and stores them in %WINDOWS%\winload.log file.
It uses its own SMTP engine and sends itself to the e-mails harvested in winload.log file (see above for the infected e-mail format).
It searches for *.exe files belonging to several antivirus/security products and attempts to overwrite them with copies of the virus.
Win32.Dumaru.B/C@mm is a mass mailer that has backdoor abilities (listens on TCP ports 1001, 2283, 10000) and also comes with a keylogger.
Attempts to terminate processes belonging to several security and antivirus programs.
On NTFS partitions, it may overwrite .exe files with copies of the virus.
It spreads using this format:
From:
[email protected]
Subject:
Use this patch immediately !
Body:
Dear friend , use this Internet Explorer patch now!
There are dangerous virus in the Internet now!
More than 500.000 already infected!
Attachment:
patch.exe
Once run, the virus does the following:
1. Creates the aforementioned files and registry keys/entries.
2. Attempts to terminate processes:
ZAUINST.EXE
ZAPRO.EXE
ZONEALARM.EXE
ZATUTOR.EXE
MINILOG.EXE
VSMON.EXE
LOCKDOWN.EXE
ANTS.EXE
FAST.EXE
GUARD.EXE
TC.EXE
SPYXX.EXE
PVIEW95.EXE
REGEDIT.EXE
DRWATSON.EXE
SYSEDIT.EXE
NSCHED32.EXE
MOOLIVE.EXE
TCA.EXE
TCM.EXE
TDS-3.EXE
SS3EDIT.EXE
UPDATE.EXE
ATCON.EXE
ATUPDATER.EXE
ATWATCH.EXE W
GFE95.EXE
POPROXY.EXE
NPROTECT.EXE
VSSTAT.EXE
VSHWIN32.EXE
NDD32.EXE
MCAGENT.EXE
MCUPDATE.EXE
WATCHDOG.EXE
TAUMON.EXE
IAMAPP.EXE
IAMSERV.EXE
LOCKDOWN2000.EXE
SPHINX.EXE
WEBSCANX.EXE
VSECOMR.EXE
PCCIOMON.EXE
ICLOAD95.EXE
ICMON.EXE
ICSUPP95.EXE
ICLOADNT.EXE
ICSUPPNT.EXE
FRW.EXE
BLACKICE.EXE
BLACKD.EXE
WRCTRL.EXE
WRADMIN.EXE
WRCTRL.EXE
PCFWALLICON.EXE
APLICA32.EXE
CFIADMIN.EXE
CFIAUDIT.EXE
CFINET32.EXE
CFINET.EXE
TDS2-98.EXE
TDS2-NT.EXE
SAFEWEB.EXE
NVARCH16.EXE
MSSMMC32.EXE
PERSFW.EXE
VSMAIN.EXE
LUALL.EXE
LUCOMSERVER.EXE
AVSYNMGR.EXE
DEFWATCH.EXE
RTVSCN95.EXE
VPC42.EXE
VPTRAY.EXE
PAVPROXY.EXE
APVXDWIN.EXE
AGENTSVR.EXE
NETSTAT.EXE
MGUI.EXE
MSCONFIG.EXE
NMAIN.EXE
NISUM.EXE
NISSERV.EXE
3. On Windows 9x/Me systems, alters win.ini and system.ini in order to run at startup.
[windows]
run=%WINDOWS%\dllreg.exe
[boot]
shell=explorer.exe %SYSTEM%\vxdmgr32.exe
4. Harvests e-mail addresses by searching inside:
.htm
.wab
.html
.dbx
.tbb
.abd
and attempts to send itself using the e-mail format described above, using its own SMTP engine and the default SMTP address.
5. Attempts to infect .exe files on NTFS partitions, but due to a bug in the search, it will only infect .exe file on the root of drives.
6. Connects to an IRC server, and joins a channel, listens on ports 1001, 10000 (TCP) for commands from an attacker. Also, port 2283 (TCP) is used as a send through (like a proxy).
7. Captures and logs the clippboard to %WINDOWS%\rundllx.sys
8. Captures and logs keystrokes (but also program name) to %WINDOWS%\vxdload.log
9. Attempts to connect to a ftp server and upload a .eml file that contains passwords and other informations.
Win32.Dumaru.Y@mm is a worm that comes by mail in the following message:
From: "Elene"
Subject: Important information for you. Read it immediately !
Body:
Hi !
Here is my photo, that you asked for yesterday.
Attachment: MYPHOTO.JPG .EXE
The worm copies itself to Windows System folder with names L32X.EXE and VXD32V.EXE and in the StartUp folder with the name DLLXW.EXE, adds the registry key:
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run\load32 = L32X.EXE
Also it adds to the shell line (in SYSTEM.INI on Windows 95, 98 and Me, or in the registry on Windows NT, 2000 and XP):
Shell = %SYSTEMDIR%\vxd32.exe
A keylogger and clipboard monitor is also installed, and the worm listens for commands on port 2283 and opens a FTP server on port 10000.
The mass-mailing component collects e-mail addresses from files with extensions .htm, .wab, .html, .dbx, .tbb, .abd and sends e-mails using its own sending engine.

 Windows 7 and above
Windows 7 and above View Screenshots(1)
View Screenshots(1) Comments
Comments

 Similar Software
Similar Software